Sponsored by Terbium Labs
Sponsored by LastPass
How Do Password Managers Fit With Other Identity and Access Management Solutions?
Sponsored by LastPass
How Does Stronger Multi-Factor Authentication Fit in With Password Managers?
Sponsored by KnowBe4
2018 Threat Impact and Endpoint Protection Report: What You Need To Know
Sponsored by CrowdStrike
Automatic Protection Against Advanced Threats
Sponsored by CrowdStrike
Aggressive, Proactive Threat Hunting
Sponsored by VASCO
A Layered Approach to Risk in Mobile Banking
Sponsored by Illusive Networks
Three Use Cases for Deception Technology in Healthcare
Sponsored by Illusive Networks
Three Use Cases for Deception Technology in Financial Services
Sponsored by Illusive Networks
A Deception Approach to Protecting ATM Networks
Sponsored by Illusive Networks
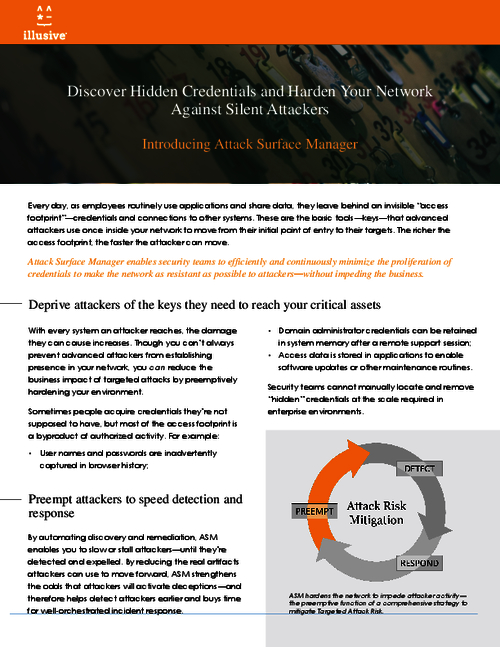
Discover Hidden Credentials and Harden Your Network Against Silent Attackers
Sponsored by Entrust Datacard
Modern Identity For The Modern Consumer
Sponsored by Entrust Datacard
Evolution of Intelligent Identity
Sponsored by Entrust Datacard
5 Ways to Ensure Digital Business Success
Sponsored by Entrust Datacard