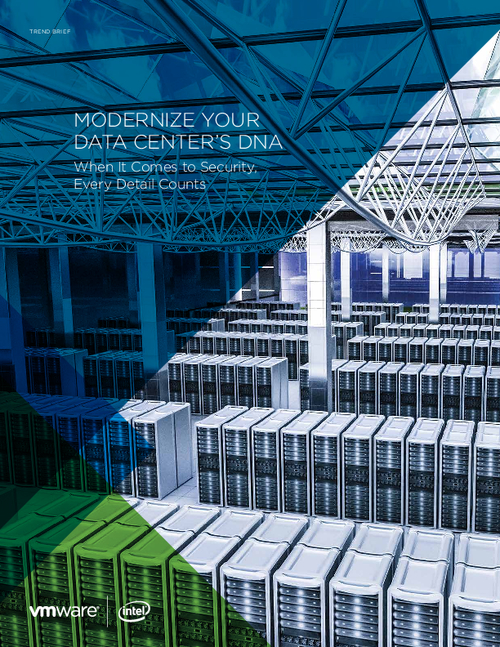
Sponsored by VMWare
Sponsored by VMWare
Planejamento para uma transformação operacional com o NSX
Sponsored by VMWare
Virtualização de redes e segurança com o VMware NSX
Sponsored by HP
The Insecurity of Network-Connected Printers
Sponsored by IBM
Magic Quadrant for Managed Security Services, Worldwide
Sponsored by IBM
2015 Cost of Data Breach Study: United States
Sponsored by IBM
How To Cut Through The Web Of Insurance Fraud
Sponsored by LOGICnow
Operationalizing Risk for Data Breach Prevention Programs
Sponsored by LOGICnow
Data Breach Risk Intelligence for CISOs
Sponsored by Spirent
The Difference Between Emulation and Simulation: Are You Testing for the Real World?
Sponsored by LogicNow
Data Breach Analytics Brief
Sponsored by LOGICnow
Data Breach Risk Intelligence
Sponsored by Sophos