Sponsored by Contrast Security
Sponsored by Early Warning
The Power of Behavioral Analytics and Anomaly Detection: Tackling the Identity Verification Challenge
Sponsored by Bishop Fox
Shifting Left: A DevSecOps Field Guide
Sponsored by Tanium
A New Class of Converged Endpoint Platforms for a Better Breed of IT SecOps
Sponsored by Mimecast
Does Office 365 Deliver The Email Security and Resilience Enterprises Need?
Sponsored by Secure Code Warrior
The Importance of Security Maturity in Development Teams
Sponsored by Secure Code Warrior
The Developer Security Maturity Matrix
Sponsored by Mimecast
Top 10 Capabilities that Organizations Need in a Secure Email Gateway: A buyer’s Guide
Sponsored by Gigamon
Ransomware Resilience & Threat Trends: Learning from History and Martial Arts
Sponsored by Gigamon
Best Practices to Maximize Application Intelligence
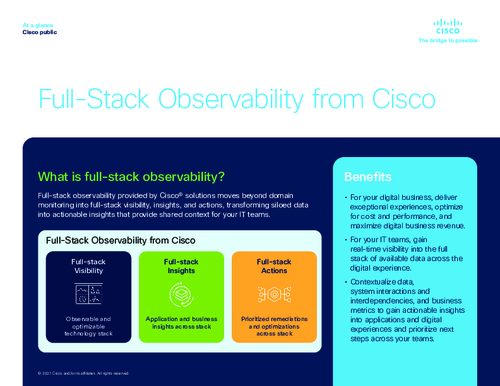
Sponsored by Cisco
Guide: How to Get Full Visibility Across Your Infrastructure
Sponsored by HelpSystems
A Breakdown of Application Security Report Results
Sponsored by Elastic Security