Sponsored by BAE Systems
Sponsored by ThreatConnect
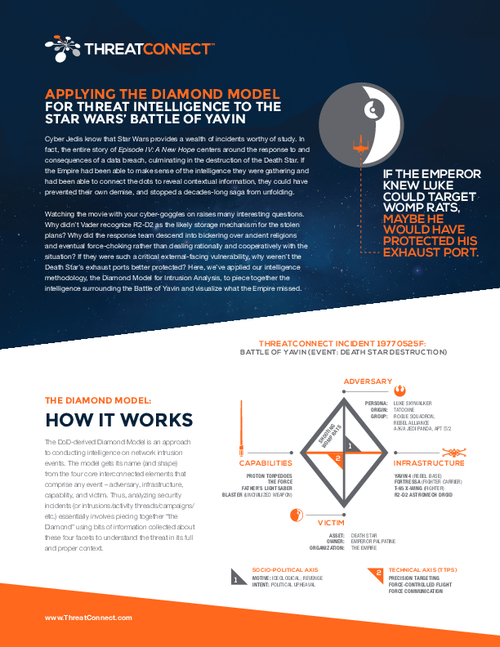
Applying Threat Intelligence to the Star Wars' Battle of Yavin
Sponsored by ThreatConnect
Threat Intelligence Platforms
Sponsored by ThreatConnect
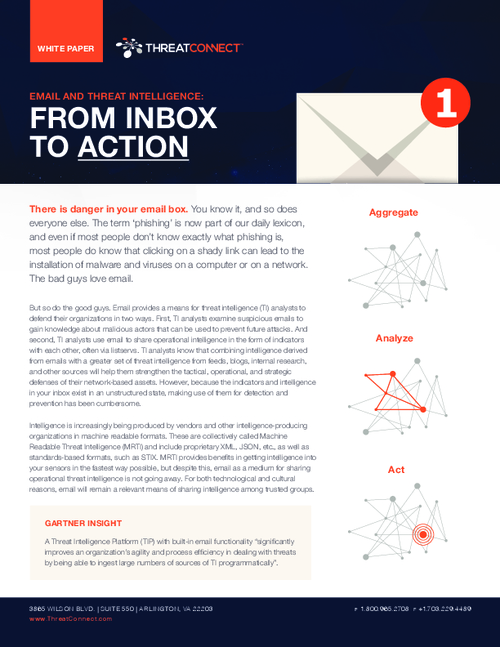
Email and Threat Intelligence: From Inbox To Action
Sponsored by Cryptzone
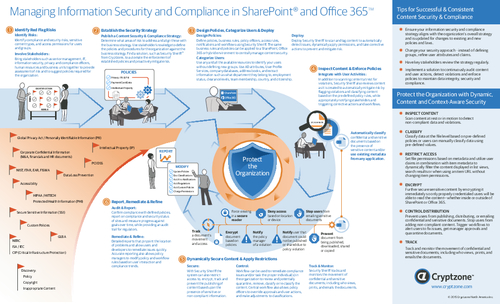
Managing Information Security And Compliance in SharePoint and Office 365
Sponsored by Cryptzone
The Aftermath Of A Breach and Steps To Reduce Risk
Sponsored by Cryptzone
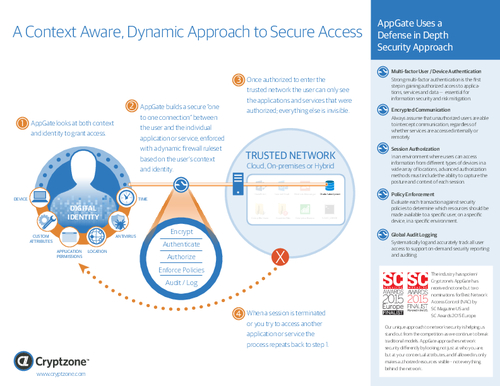
A Context-Aware, Dynamic Approach To Secure Access
Sponsored by Cryptzone
Four Steps To Readily Achievable Web Accessibility
Sponsored by Cryptzone
After the Perimeter: How A 'Segment of One' Simplifies And Improves Security
Sponsored by IBM
New Counter-Fraud Strategies
Sponsored by ThreatTrack
Detecting Anomalous Behavior: A New Strategy
Sponsored by ISMG
PCI Compliance in the Cloud
Sponsored by Akamai
Internet Anonymity: Pros and Cons of the Tor Network
Sponsored by Akamai
5 Technologies to Enable Digital Transformation
Sponsored by Akamai