Sponsored by RSA
Sponsored by Malwarebytes
How To Protect Your Business From Ransomware
Sponsored by IBM
Battling Fraud at the Root Cause
Sponsored by Veriato
Conversational User Behavior Analytics
Sponsored by Recorded Future
50 Shades of Dark: How to Use the Dark Web for Threat Intelligence
Sponsored by Recorded Future
Understand Your Attacker: A Practical Guide to Identifying TTPs With Threat Intelligence
Sponsored by Recorded Future
How to Produce a World-Class Threat Intelligence Capability
Sponsored by Prevalent
Vendor Risk Management: Getting it Right
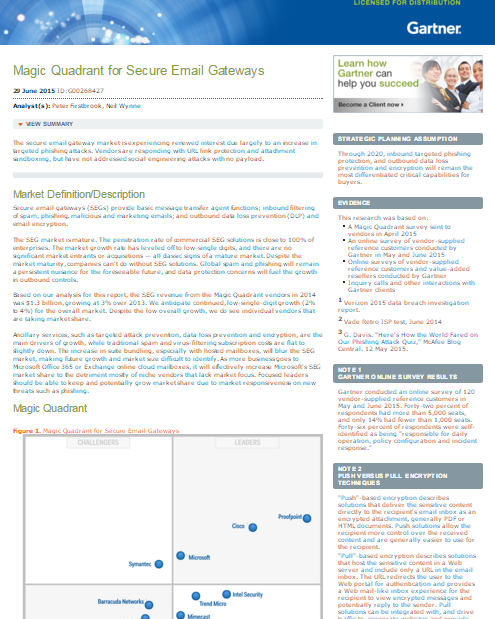
Sponsored by Proofpoint
Gartner Magic Quadrant for Secure Email Gateways, 2015
Sponsored by Proofpoint
Enterprise Threat: The Human Factor
Sponsored by Proofpoint
How Risky Mobile Apps Steal Data and Spy on Users
Sponsored by Proofpoint
Accelerating Office365 Adoption with Security and Compliance Controls
Sponsored by Carbon Black
How Vulnerable is Your Endpoint Software?
Sponsored by IBM
The Case For Security Intelligence Services, Hosted From The Cloud
Sponsored by IBM