Sponsored by Anomali
Sponsored by F5
Fraud Prevention Without Friction
Sponsored by Entrust
Digital Documentation: Authenticity and Integrity
Sponsored by F-Secure
Balancing Protection and Profit
Sponsored by LastPass
Psychology of Passwords
Sponsored by Veeam
Ransomware: Shift from Detection to Protection
Sponsored by Checkmarx
DAZN Case Study: Why Securing Open Source is Essential
Sponsored by Graylog
Automating Security Operations
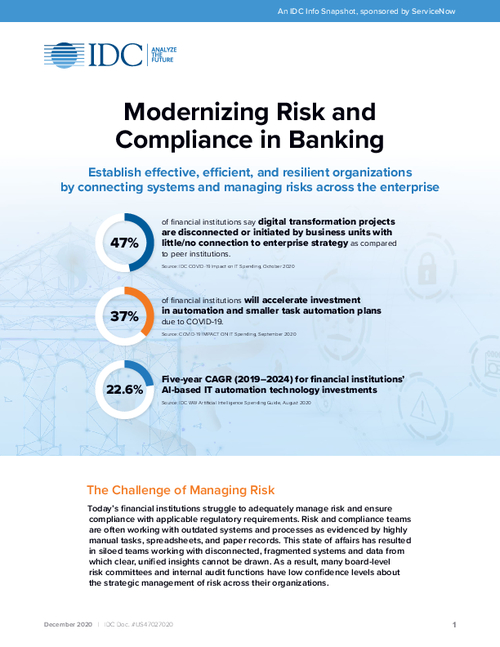
Sponsored by ServiceNow
IDC Snapshot: Modernizing Risk and Compliance in Banking
Sponsored by ServiceNow
Risk Management Use Cases in Financial Services
Sponsored by Symphony Ayasdi
Exposing Financial Crime with Full Transparency
Sponsored by Expel
How to Get Started with the NIST Cybersecurity Framework (CSF)
Sponsored by Synopsys
Shifting Left to Accelerate Security Approvals for ATOs in Defense Programs
Sponsored by Cofense
Phish Are Getting To Your Inbox: Why Your “Secure” Email Gateway Isn’t
Sponsored by Cofense