Sponsored by Open Raven
Sponsored by Pondurance
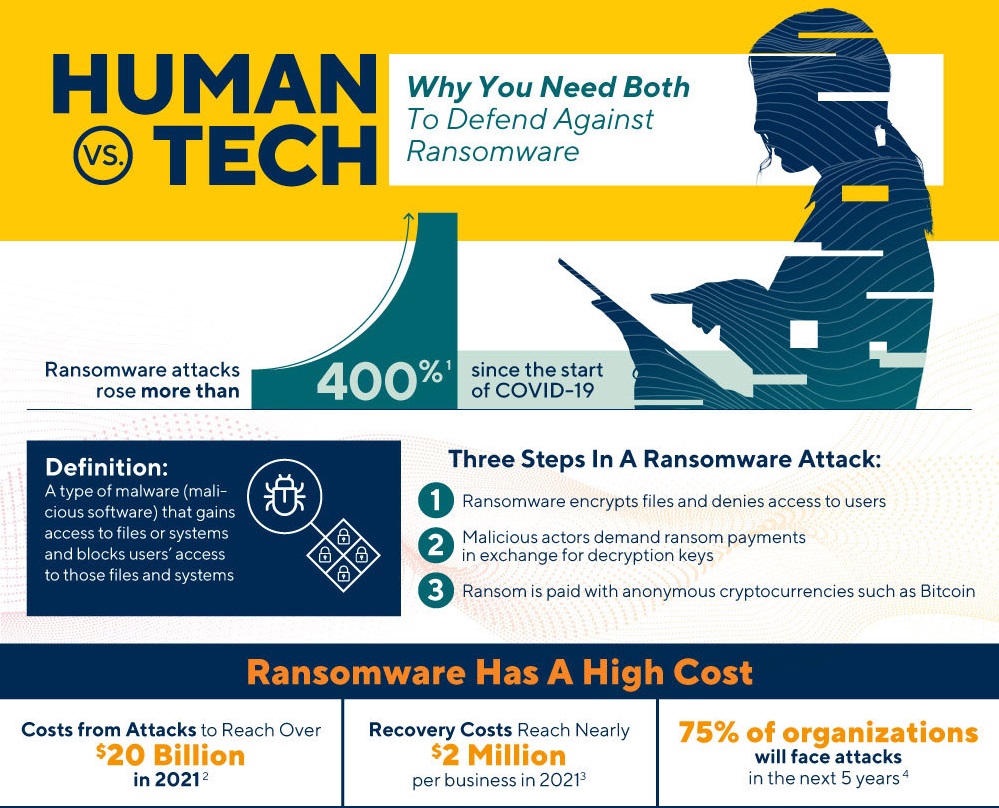
Human vs. Tech: Why You Need Both to Defend Against Ransomware
Sponsored by Abnormal Security
CISO Guide to Vendor Email Compromise (VEC) - The Risk of VEC and How to Stop It
Sponsored by LogicGate
The Definitive Guide to Risk Quantification
Sponsored by Gigamon
2021 Cyberthreat Defense Report
Sponsored by LexisNexis
Respond to Fraud in Milliseconds
Sponsored by Cofense
Cofense Q3 2021 Phishing Review - MSP Insights
Sponsored by Sophos
The State of Ransomware in Finance 2021
Sponsored by Sophos
The State of Ransomware in Manufacturing and Production 2021
Sponsored by Proofpoint
The Human Factor 2021
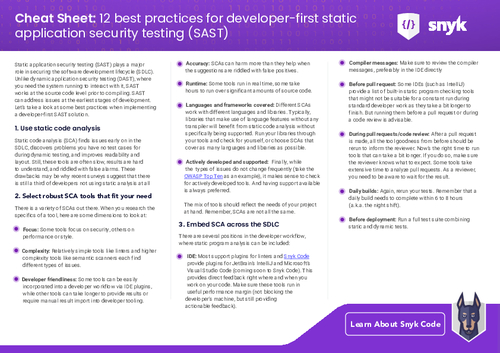
Sponsored by Snyk