Sponsored by Vasco
Sponsored by IBM
Content Enabling the Mobile Workforce
Sponsored by Good Technology
BYOD Policy Consideration: Security, Privacy, Acceptable Use and Expense
Sponsored by Good Technology
5 Critical Steps to Securely Manage Mobile Apps and Devices
Sponsored by Good Technology
Mobile App Security Using Containerization
Sponsored by Good Technology
Secure Mobility: Critical Container Requirements
Sponsored by Fiberlink
Financial Mobility: Balancing Security and Success
Sponsored by Blackberry
The Secret Ingredient in Mobile ROI: Why Security is Paramount
Sponsored by Blackberry
The Top 8 Mobile Security Risks: How to Protect Your Organization
Sponsored by Blackberry
Enabling Mobile Users and Staying Compliant: How Healthcare Organizations Manage Both
Sponsored by Blackberry
Mobility in Financial Services: A Checklist Towards Regulatory Compliance
Sponsored by IBM
IBM X-Force Threat Intelligence Quarterly 4Q 2014
Sponsored by IBM
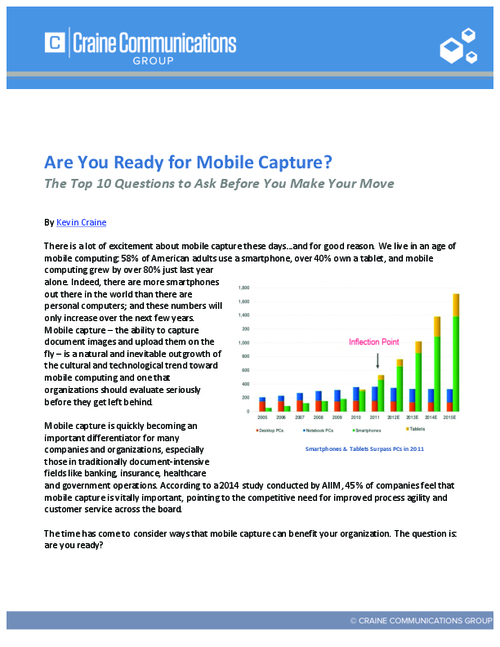
Are You Ready for Mobile Capture?
Sponsored by RSA
Countering Cyber Threats with Behavioral Analytics
Sponsored by Symantec