Cyberwarfare / Nation-State Attacks , Forensics , Fraud Management & Cybercrime
White House Preparing 'Executive Action' After SolarWinds Attack
Deputy National Security Adviser Anne Neuberger Offers an Update on Investigation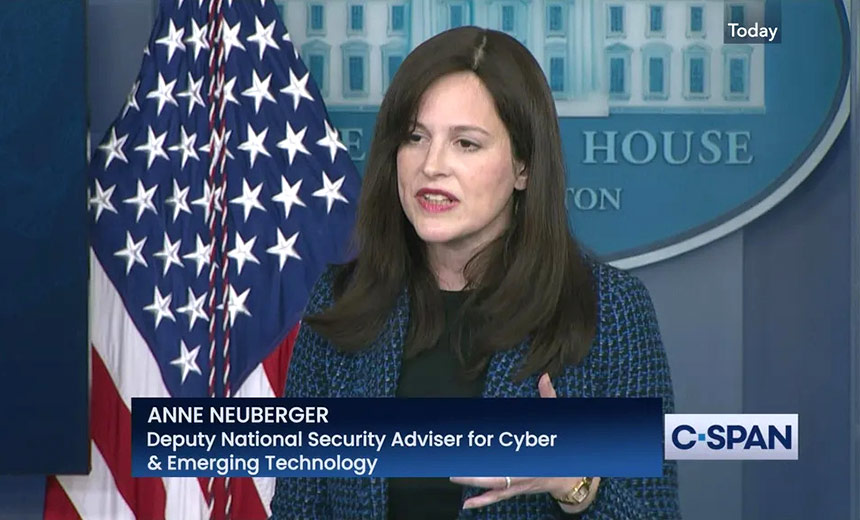
In an update on the investigation into the SolarWinds supply chain attack, Deputy National Security Adviser Anne Neuberger said the Biden administration is preparing "executive action" to address security shortcomings that have come to light.
See Also: Enabling Government for Modernized IT
"We're working on close to about a dozen things - likely eight will pass - that will be part of an upcoming executive action to address the gaps we’ve identified in our review of this incident," Neuberger said.
Neuberger, who was recently named coordinator of the investigation into the attack, made her comments Wednesday at a White House press briefing.
Investigators believe that nine federal agencies, as well as 100 private sector organizations, were compromised as part of the attack, Neuberger said.
The supply chain attack was launched when hackers planted a backdoor known as "Sunburst" within an update for SolarWinds' Orion network monitoring platform. Then, 18,000 of the company's customers downloaded the update, and some of those were further targeted for follow-on attacks.
Neuberger also noted that it will take several months to fully expel malicious code from the networks targeted by the hackers.
Assessing the entire scope of the SolarWinds attack is difficult, Neuberger acknowledged.
"There's a lack of domestic visibility, so as a country, we choose to have both privacy and security," Neuberger said. "So the intelligence community largely has no visibility into private sector networks. The hackers launched the hack from inside the United States, which further made it difficult for the U.S. government to observe their activity. Even within federal networks, a culture and authorities inhibit visibility, which is something we need to address."
The agencies investigating the SolarWinds supply chain attack have said it likely was part of a cyberespionage campaign conducted by a hacking group with ties to Russia (see: President Biden Orders SolarWinds Intelligence Assessment).
Executive Action
Neuberger did not offer specifics about what any White House executive action might contain. But security experts note that the Biden White House could enact several measures to address the cybersecurity concerns stemming from this hacking incident.
Tom Kellermann, who is head of cybersecurity strategy for VMware and a member of the Cyber Investigations Advisory Board for the U.S. Secret Service, suggests that the Biden administration should change the structure of federal agencies and have department CISOs report directly to the secretary, which would give leadership better access to information on cyberthreats.
"Since the position of the CISO was created, most report to the chief information officers within organizations. However, the CISO-to-CIO reporting structure represents a potential governance crisis," Kellermann says. "The defensive mindset of the CISO often conflicts with the uptime, availability and content-driven goals of CIOs. Another concern relating to this structure is that cybersecurity measures may come second."
The Biden administration also should call for the implementation of threat hunting across federal networks - as well as managed service providers that supply IT and networking services to agencies - to better detect security flaws and identify hacking attempts, Kellermann says. The White House could mandate that network detection and response platforms must be integrated with endpoint protection platforms to add another layer of protection, he adds.
Kellermann also calls on Biden to respond to the threat groups responsible for this and other hacking attempts.
"I would recommend immediate proportionate cyber response against Turla, Sandworm and APT28 and APT29," Kellermann says, referring to several hacking groups with apparent ties to Russia.
President Biden's $1.9 trillion proposal for COVID-19 economic relief includes $9 billion to improve cybersecurity at the federal level. Of that, $690 million would pay for a Cybersecurity and Infrastructure Security Agency project designed to improve monitoring and incident response across government agencies (see: Biden's $10 Billion Cybersecurity Proposal: Is It Enough?).
Darren Hayes, associate professor at the Seidenberg School of Computer Science and Information Systems at Pace University in New York, also notes that the U.S. government could impose economic or other sanctions against those it deems responsible for the SolarWinds attack.
"The Biden administration should strongly consider increased sanctions," Hayes says. "Attribution for cyberattacks were historically problematic, especially because countries like China and Russia would use unofficial groups in their country to launch these attacks. Ultimately, we know that these governments have sanctioned cyberattacks that align with their policies."
Microsoft Update
On Thursday, Microsoft, which was one of several tech companies affected by the SolarWinds supply chain follow-on attacks, published a final assessment of its own investigation.
The company says that none of its internal systems were used as launching points to attack other targets and that hackers never accessed the vast majority of Microsoft's source code. When some code repositories were accessed, the attackers only accessed a limited number of files, the company says.
The hackers gained access to some of the code used for certain components of Microsoft's Azure, Intune and Exchange products, according to the Thursday update.
"The search terms used by the actor indicate the expected focus on attempting to find secrets," Microsoft says in its update. "Our development policy prohibits secrets in code, and we run automated tools to verify compliance. Because of the detected activity, we immediately initiated a verification process for current and historical branches of the repositories."
Concerns About Security Shortcomings
On Feb. 9, Sens. Mark Warner and Marco Rubio sent letters to the FBI, the Office of the Director of National Intelligence, the U.S. National Security Administration and CISA, criticizing the lack of coordination of the agencies' joint SolarWinds investigation. Then, the White House officially announced that Neuberger was serving as the point person for the probe (see: White House Taps Neuberger to Lead SolarWinds Probe).
During Wednesday's briefing, Neuberger noted that the federal government is developing ways to mitigate hacking risks and address government security shortcomings as cited by the two senators.
"One of the things we've done from the White House is coordinate a set of questions to assess that and pull that piece together," Neuberger said. "It varies agency by agency. And certainly, there is a national security impact, and that is what we're looking to consider - both how we manage the risk of that and how we address it for the future."
On Thursday, Rubio and Warner announced that the Senate Intelligence Committee will hold a public hearing about the SolarWinds supply chain attack on Tuesday. Witnesses will include executives from SolarWinds, Microsoft, CrowdStrike and FireEye.