Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Governance & Risk Management
US Cyber Command Alert: Patch Palo Alto Networks Products
'Critical' Authentication Bypass Risk Posed by Easy-to-Exploit PAN-OS Software Flaw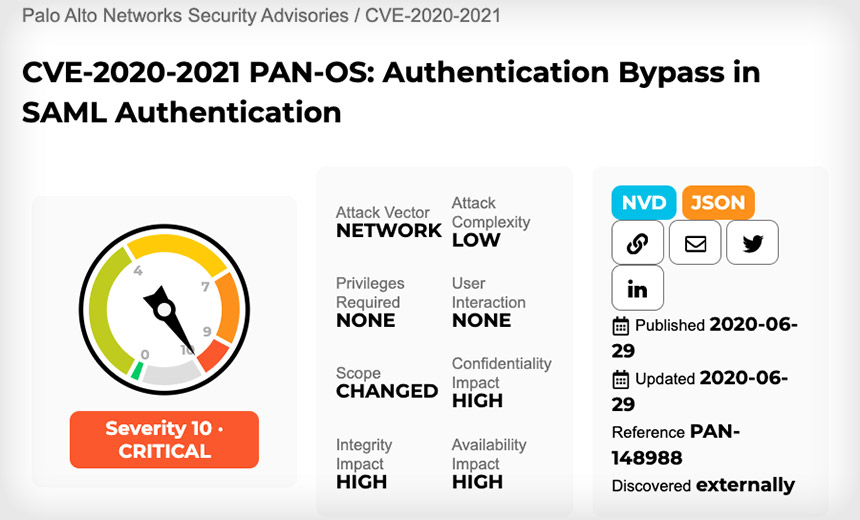
All Palo Alto Networks users are being warned to update their products to patch a "critical" flaw that can be remotely exploited to bypass authentication and take full control of systems or gain access to networks.
See Also: Enabling Government for Modernized IT
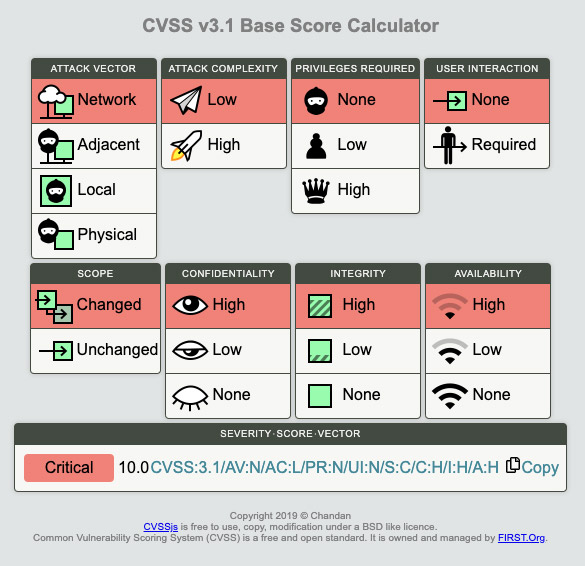
The flaw, designated CVE-2020-2021, exists in how the PAN-OS software that runs Palo Alto devices implements Security Assertion Markup Language. Because of the flaw, remote attackers could be able to bypass authentication and execute arbitrary code on vulnerable systems, paving the way for a full compromise of an organization's network and systems.
Palo Alto issued security updates Monday that fix the flaw, as well as detailed workarounds.
"An unauthenticated attacker with network access could exploit this vulnerability to obtain sensitive information," U.S. Cybersecurity and Infrastructure Security Agency warns.
"Please patch all devices affected by CVE-2020-2021 immediately, especially if SAML is in use," U.S. Cyber Command says in a Monday cybersecurity alert, which praises Palo Alto for moving quickly to issue security updates.
"Foreign APTs will likely attempt exploit soon," the alert adds, referring to advanced persistent threat groups, which typically means hacking teams affiliated or run by nation-states (see: NSA Is Latest Intelligence Agency to Sound VPN Patch Alarm).
Palo Alto Networks says users are at risk if two conditions are met. "When Security Assertion Markup Language (SAML) authentication is enabled and the 'Validate Identity Provider Certificate' option is disabled (unchecked), improper verification of signatures in PAN-OS SAML authentication enables an unauthenticated network-based attacker to access protected resources."
Flaw in PAN-OS
All recent versions of PAN-OS have the vulnerability. "This issue affects PAN-OS 9.1 versions earlier than PAN-OS 9.1.3, PAN-OS 9.0 versions earlier than PAN-OS 9.0.9, PAN-OS 8.1 versions earlier than PAN-OS 8.1.15, and all versions of PAN-OS 8.0 (EOL)," Palo Alto says. "This issue does not affect PAN-OS 7.1."
Updated versions of the vulnerable PAN-OS software, issued Monday by Palo Alto, that have been patched to fix the flaw are "PAN-OS 8.1.15, PAN-OS 9.0.9, PAN-OS 9.1.3, and all later versions," the vendor says.
Palo Alto products that are at risk - because they can be protected using SAML-based single sign-on - include:
- GlobalProtect Gateway;
- GlobalProtect Portal;
- GlobalProtect Clientless VPN;
- Authentication and Captive Portal;
- PAN-OS next-generation firewalls (PA-Series, VM-Series) and Panorama web interfaces;
- Prisma Access.
"In the case of GlobalProtect Gateways, GlobalProtect Portal, Clientless VPN, Captive Portal, and Prisma Access, an unauthenticated attacker with network access to the affected servers can gain access to protected resources if allowed by configured authentication and security policies," Palo Alto says in its security alert.
"In the case of PAN-OS and Panorama web interfaces, this issue allows an unauthenticated attacker with network access to the PAN-OS or Panorama web interfaces to log in as an administrator and perform administrative actions," it adds. "In the worst-case scenario, this is a critical severity vulnerability with a CVSS Base Score of 10.0."
No Active Attacks Seen - Yet
The good news: "Palo Alto Networks is not aware of any malicious attempts to exploit this vulnerability."
In addition, there's a straightforward workaround that can be used to immediately mitigate the flaw until the updates can be installed. "This issue cannot be exploited if the 'Validate Identity Provider Certificate' option is enabled in the SAML Identity Provider Server Profile," Palo Alto says.
But Will Dormann, a vulnerability analyst at the CERT Coordination Center - the coordination center of the computer emergency response team for the Software Engineering Institute - warns that some vendors require that the "validate identity provider certificate" option be disabled.
Palo Alto (PAN-OS) servers are vulnerable to CVE-2020-2021 if:
— Bad Packets (@bad_packets) June 29, 2020
SAML authentication is enabled
'Validate Identity Provider Certificate' option is disabled*
* Required per multiple vendors (https://t.co/pePMkimPZT)
https://t.co/DxqzxvnnT5
Troy Mursch of the Chicago-based threat intelligence firm Bad Packets says his firm has been scanning the internet for vulnerable systems and directly alerting countries' computer emergency response/readiness teams and information sharing and analysis centers so they can directly notify domestic organizations that have vulnerable systems.
Critical Flaw Poses Serious Risk
Experts say the severity of the vulnerability and risk it poses should not be underestimated. The flaw is rated as being "critical," meaning it can be easily exploited by remote attackers to compromise vulnerable systems, and potentially use them to gain access to corporate networks and data.
Rob Joyce, the senior adviser for cybersecurity strategy to the director of the U.S. National Security Agency, says organizations should prioritize patching this flaw by updating all devices to the latest Palo Alto operation system as quickly as possible.
"Critical authentication bypass on Palo Alto Networks firewalls and corporate VPNs," Joyce tweets. "Need to update to latest OS. There are not many vulnerabilities assigned a 10 out of 10 score (CVE-2020-2021)."
'Digital Signature Validation Issue'
Credit for discovering and reporting the flaw, Palo Alto says, goes to Salman Khan from the cyber risk and resilience team and Cameron Duck from the identity services team at Monash University in Melbourne, Australia.
"The problem is that [Palo Alto] has a digital signature validation issue which allows modification of the assertion containing the information about who was authenticated," tweets Ryan Newington, who was part of the team that discovered the flaw.
Bad Packets' Mursch says that if past flaws in widely used networking gear are any indication, attackers will already be scanning for vulnerable Palo Alto systems to try and exploit them.
For comparison's sake, he notes that mass scanning continues as attackers attempt to find flaws for vulnerabilities that were long ago patched, but for which organizations have yet to install the updates. He says that's especially true for a vulnerability in Pulse Secure VPN SSL servers (CVE-2019-11510), which was patched in May 2019, and a separate flaw in Citrix Application Deliver Controller and Gateway products (CVE-2019-19781), which was fixed in January (see: Hacked Law Firm May Have Had Unpatched Pulse Secure VPN).
Mass scanning activity detected from 213.169.148.152 checking for Pulse Secure VPN servers vulnerable to CVE-2019-11510 (https://t.co/lXcedIyQSB). #threatintel pic.twitter.com/v2rYKxKcR1
— Bad Packets (@bad_packets) June 29, 2020
"If CVE-2019-11510 and CVE-2019-19781 have taught us anything, you should patch CVE-2020-2021 ASAP," Mursch tweets.