Endpoint Security , Fraud Management & Cybercrime , Next-Generation Technologies & Secure Development
WannaCry Probe: Scotland, Wales and Northern Ireland React
Ransomware Hit NHS Scotland Hard; Northern Ireland and Wales Escaped Infections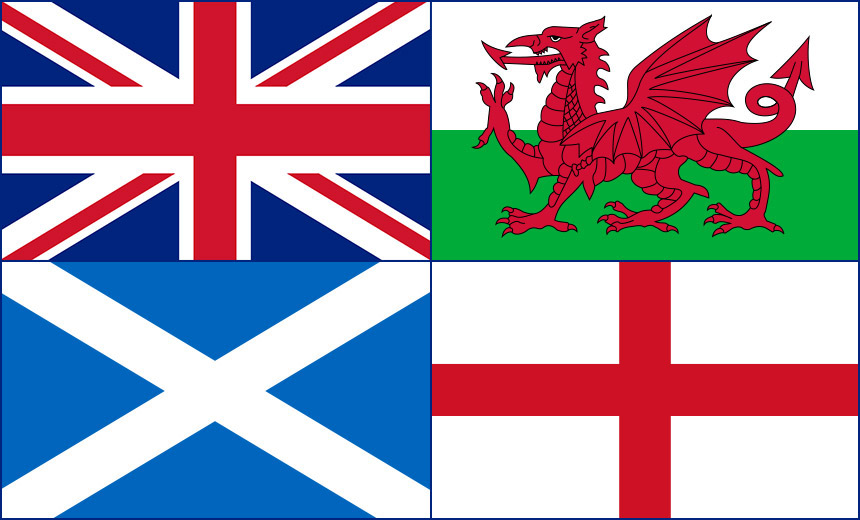
The United Kingdom might be greater than the sum of its parts. But when it came to the WannaCry outbreak, some parts of the United Kingdom did less great than others.
See Also: The Cybersecurity Swiss Army Knife for Info Guardians: ISO/IEC 27001
On Friday, Parliament's independent National Audit Office published the results of its probe into how the WannaCry outbreak impacted NHS England and found blame with both that organization and the U.K. government's Department of Health (see Postmortem Finds NHS 'Could Have Prevented' WannaCry).
In the United Kingdom, many aspects of health are devolved, meaning they're controlled separately by each of the national governments within the United Kingdom.
Different U.K. nations' governments and health services appear to have practiced different levels of preparation.
In addition to NHS England, NHS Scotland, which provides both health and social care services, also was hit hard by WannaCry. But the "NHS" in Northern Ireland, known as Health & Social Care Services, tells me that it escaped the WannaCry outbreak with no infections. So too did NHS Wales, although it took the precautionary measure of blocking all external emails after the WannaCry outbreak while it reviewed all systems' updates and patches.
Size may have been a factor in escaping the WannaCry outbreak. England is by far the biggest U.K. nation, with an estimated population of 55.2 million, compared with 5.4 million in Scotland, 3.1 million in Wales and 1.9 million in Northern Ireland. Bigger nations' health boards have bigger IT footprints, which may be harder to keep secure. Any cybersecurity failures may also be magnified throughout the bigger organizations (see Post-WannaCry, UK Promises NHS England a Funding Injection).
Regardless, what lessons might the governments and health boards of Scotland, Wales and Northern Ireland be taking away from the WannaCry outbreak and NAO findings to apply to their own health services?
Northern Ireland Responds
"We welcome the National Audit Office's findings and the learnings this provides for us to support our cybersecurity and response planning," a spokeswoman for Northern Ireland's Health and Social Care Board tells me.
"The NAO report is specific to the NHS in England. However, DoH [Department of Health] NI has made additional immediate investment to improve cybersecurity resilience. The HSC [Health and Social Care] eHealth team is working with the HSC Business Services Organization [BSO] to support health and social care organizations to further strengthen cyber resilience and to strengthen business continuity plans in the event of further attacks," she says.
The Northern Ireland government says it also maintains "centers of excellence" designed to improve cybersecurity practices. "DoH and HSC are part of an NI cybersecurity forum and share learning and maintain communications with NHS and other national centers of expertise to support the HSC process of improving cybersecurity and response plans," the spokeswoman says.
Wales: No Impact
The government of Wales declined to comment on the NAO's WannaCry report, except to note that it suffered no infections. But after WannaCry began infecting systems on May 12, NHS Wales began blocking all external emails sent to NHS Wales as a precaution, as well as applying the latest anti-virus signatures and any outstanding updates to all of its systems.
On May 16, Carwyn Jones, the first minister of Wales, said in a statement that "the ransomware has not affected the integrity of NHS systems here in Wales, partly due to the resilience defenses already in place."
His statement suggests that incoming WannaCry infections were detected but blocked. "Where the ransomware has been detected, immediate remedial action has been taken to prevent the spreading of the virus. This has ensured that no patient data has been compromised or lost," he said.
While there were some disruptions as a result of the outbreak, Jones said they were minimal. "We have no reports of the incident impacting on patient care," he said.
Jones added that no WannaCry infections had been reported in Welsh government, local government bodies or schools' systems.
WannaCry Slammed NHS Scotland
Scotland, however, was hit hard by WannaCry.
Reacting to the NAO probe findings, the Scottish government tells me that plans are underway for NHS boards to gain greater visibility into their information security postures. "NHS boards in Scotland are implementing an information security management system to minimize risk and ensure business continuity by proactively limiting the impact of a security breach," a Scottish government spokeswoman tells me.
The government also highlighted how many pounds it spends on cybersecurity. "The Scottish government provides £100 million ($132 million) per annum to health boards for IT investment and cyber security resilience," the spokeswoman says. "Health boards spend at least the same amount per annum. However, we know that in 2016/17 total spend was around £257 million [$340 million]."
Even so, WannaCry disrupted 11 of Scotland's 14 territorial health boards and two of its eight special health boards, authorities say. NHS Scotland estimates that fewer than 600 appointments had to be canceled or rescheduled as a result of WannaCry. The government has not estimated how many general practitioners - doctors' offices - may have been affected or had to reschedule appointments.
Scotland Seeks Information Security Management System
Responding to the NAO report, a spokeswoman for NHS Scotland described changes being made by its eHealth group, which addresses digital policy and strategy, technical strategy and governance as well as information assurance, that will hopefully blunt future attacks.
For starters, eHealth is leading the ISMS push, "which will provide greater resilience, as well as central monitoring and control across NHS infrastructure," the spokeswoman for Scotland's Health and Sport Department tells me.
The ISMS effort appears to have been underway for at least two years, and no deadline for the effort appears to have been set.
Scottish Action Plan Due in November
The Scottish government is also preparing a new action plan for all public sector organizations. "A range of security measures is in place to ensure the public sector can respond appropriately to cyberattacks," the spokeswoman says. "A further action plan to be published in November will help promote a common approach to cyber resilience across Scotland's public bodies."
The spokeswoman also notes that NHS Scotland "currently implements an information security policy framework aligned to the global industry standards ISO/IEC 27001 and 27002 that defines a system of security controls and continual improvement to manage information risk, to keep information safe and keep NHS systems running."
The Scottish government didn't immediately respond to a request for information on when that project - or the ISMS project - was launched or what deadline has been set.
To date, however, it appears that only one trust, NHS Fife, has achieved ISO 27001 compliance.
Whether these planned changes and improvements will be enough to blunt the next major cyberattack or malware outbreak of WannaCry proportions - or worse - remains to be tested.











